
Loading ...
-
What do I ALWAYS say DO NOT USE? ANYTHING ADOBE! ".pdf" LOL
Or just UPGRADE to Linux no more worries.
Researchers have demonstrated a novel class of attacks that could allow a bad actor to potentially circumvent existing countermeasures and break the... moreWhat do I ALWAYS say DO NOT USE? ANYTHING ADOBE! ".pdf" LOL
Or just UPGRADE to Linux no more worries.
Researchers have demonstrated a novel class of attacks that could allow a bad actor to potentially circumvent existing countermeasures and break the integrity protection of digitally signed PDF documents.
Called "Shadow attacks" by academics from Ruhr-University Bochum, the technique uses the "enormous flexibility provided by the PDF specification so that shadow documents remain standard-compliant." less
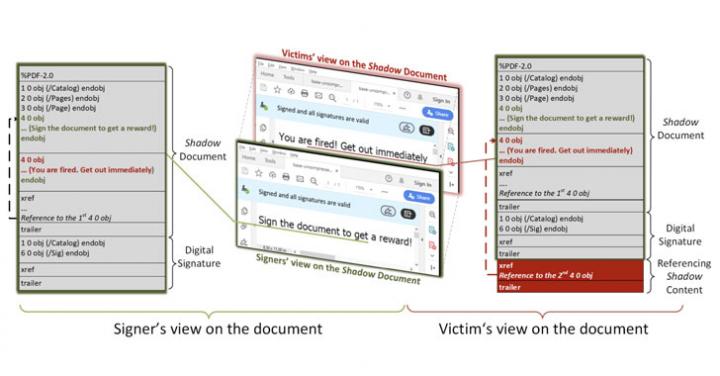
Researchers demonstrated Shadow attacks that could allow hackers to break the integrity protection of digitally signed PDF documents.

Loading ...
There are no more posts to show.


 Loading ...
Loading ... Loading ...
Loading ...